Written by: Alexandra Bretschneider, CCIC, Cyber Practice Leader | Johnson, Kendall & Johnson
With the pervasive use of technology in business operations, Cyber has quickly risen in the ranks of greatest threats facing businesses across all industries today. Often, organizations are unsure where to start when it comes to managing Cyber Risk. The purpose of this post is to provide guidance on some key areas to improve your organization’s Cyber Risk posture.
Ultimately, it is up to each organization to decide where to focus their time & investment in managing Cyber Risk. You should start by asking yourself…
What or which Cyber Risk Management practices and strategies are reasonable to expect of an organization like mine?
Would you expect an organization of your peer group to have conducted employee trainings, vulnerability & penetration assessments? Would you have expected an organization like mine to have conducted a third-party risk assessment? Would you expect us to have an Incident Response policy in place, and furthermore, to have tested it?
The answers to these questions are subjective and will vary by organization. But documenting your thought process around what constitutes a reasonable Cyber Risk Management program may provide critical towards your defense in the court of law.
A “cyber incident” can take many shapes, including a Phishing or Social Engineering attack, Ransomware/Extortion event, Denial of Service attack, a Hacking attempt aimed at obtaining private or confidential information, etc. The cost of global cybercrime is estimated to be over $400 billion annually. As the risks increase in pervasiveness, so does the Government regulation.
With privacy laws passed in all 50 states (each different in their own right), in addition to several international laws, compliance is critically important.
And just the same as a cyber incident, a Cyber Risk Management Program will include many parts, across people, processes, and technology.
One key component of a comprehensive Cyber Risk Management is the procurement of a CYBER INSURANCE policy. JKJ’s Cyber Practice includes developing expertise in the varied landscape of cyber insurance product offerings, as coverage differences are nuanced and inconsistent across the market. JKJ has established relationships with the top tier insurance carriers in the marketplace, both domestically and from Lloyds of London. JKJ developed a proprietary cyber insurance program designed specifically for our clients to address their unique exposures.
As part of buying cyber insurance, the insured receives the benefit from a well-orchestrated incident handling team, lead by a “Breach Coach” – also known as a Privacy Attorney. The Privacy Attorney or Breach Coach will guide the actions taken to address a potential or confirmed cyber incident, under the protection of attorney-client privilege. They will orchestrate the securing of an IT Forensics team, Public Relations firm, and other resources, such as notification services or call centers, as appropriate.
Additionally, Cyber Insurance carriers offer fairly robust tools and services either complimentary or discounted when a policy is bound. These may include Employee Trainings, Phishing Exercises, Incident Response templates, Password Management resources, Dark Web scans, and more. Your JKJ team can assist you in understanding what services are available from your Cyber Insurance carrier.
JKJ is a member of TechAssure. TechAssure is global network comprised of carefully selected brokerages that specialize in risk management for clients that create, manufacture, sell or service technology-based products or services all over the world. As a TechAssure member, JKJ is able to provide exclusive benchmarking data, including coverage & cost information.
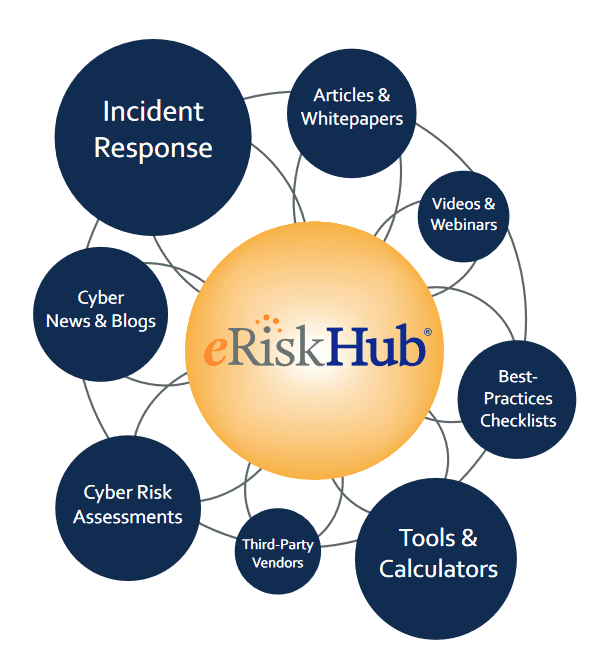
Through this membership JKJ affords our clients unique access to the most robust cyber risk management platform available: the NetDiligence eRiskHub. Through this hub and a variety of relationships with firms focused on PRE and POST breach services, JKJ can assist with the risk management strategies that will improve your organization’s Cyber Risk posture.
If you have any questions or if you would like to discuss your cyber risk management program, please complete the form below: